A newly discovered Linux malware known as Symbiote infects all running processes on compromised systems, steals account credentials, and gives its operators backdoor access.
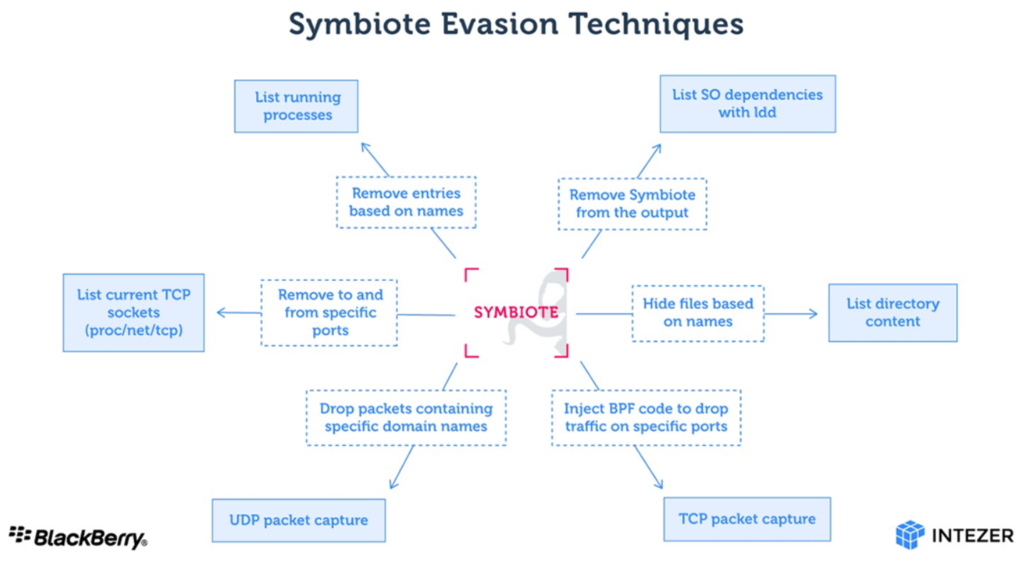
Unlike other Linux threats, Symbiote needs to infect other running processes to inflict damage on the compromised machines. It is a shared object (SO) library that is loaded into all running processes using LD_PRELOAD (T1574.006), and like a parasite infects the machine. Once the malware has infected all the running processes, it provides the threat actor with rootkit capability and supports data-stealing capabilities. A file with the. SO file extension is a Shared Library file. likewise .dll file format for windows.
Once the malware has infected a machine, it hides itself and any other malware used by the threat actor, making infections very hard to detect. Performing live forensics on an infected machine may not turn anything up since all the file, processes, and network artifacts are hidden by the malware.
In addition to the rootkit capability, the malware provides a backdoor for the threat actor to log in as any user on the machine with a hardcoded password, and to execute commands with the highest privileges.” reads the report published by Blackberry. “Since it is extremely evasive, a Symbiote infection is likely to “fly under the radar.” In our research, we haven’t found enough evidence to determine whether Symbiote is being used in highly targeted or broad attacks.
Experts reported that one interesting technical feature implemented by Symbiote is the Berkeley Packet Filter (BPF) hooking functionality, it is the first Linux malware to use this feature to hide malicious network traffic.
When an administrator starts any packet capture tool on the infected machine, BPF bytecode is injected into the kernel that defines which packets should be captured. In this process, Symbiote adds its bytecode first so it can filter out network traffic that it doesn’t want the packet-capturing software to see.
Symbiote is a malware that is highly evasive. Its main objective is to capture credentials and to facilitate backdoor access to infected machines. Since the malware operates as a userland level rootkit, detecting an infection may be difficult.” concludes the report. “Network telemetry can be used to detect anomalous DNS requests, and security tools such as antivirus and endpoint detection and response (EDR) should be statically linked to ensure they are not “infected” by userland rootkits.
Indicators of Compromise (IoCs)
Hashes
| Hash | Notes |
| 121157e0fcb728eb8a23b55457e89d45d76aa3b7d01d3d49105890a00662c924 | “kerneldev.so.bkp.” Appears to be an early development build. |
| f55af21f69a183fb8550ac60f392b05df14aa01d7ffe9f28bc48a118dc110b4c | “mt64_.so.” Missing credential exfiltration over DNS. |
| ec67bbdf55d3679fca72d3c814186ff4646dd779a862999c82c6faa8e6615180 | “search.so.” First sample with credential exfiltration of DNS. |
| a0cd554c35dee3fed3d1607dc18debd1296faaee29b5bd77ff83ab6956a6f9d6 | “liblinux.so.” |
| 45eacba032367db7f3b031e5d9df10b30d01664f24da6847322f6af1fd8e7f01 | “certbotx64.” dnscat2 |
Ports Hidden
- 45345
- 34535
- 64543
- 24645
- 47623
- 62537
- 43253
- 43753
- 63424
- 26424
Domains Hidden
- assets[.]fans
- caixa[.]cx
- dpf[.]fm
- bancodobrasil[.]dev
- cctdcapllx0520
- cctdcapllx0520[.]df[.]caixa
- webfirewall[.]caixa[.]wf
- caixa[.]wf
Process Names Hidden
- javaserverx64
- javaclientex64
- javanodex86
- apache2start
- apache2stop
- [watchdog/0]
- certbotx64
- certbotx86
- javautils
File Names Hidden
- apache2start
- apache2stop
- profiles.php
- 404erro.php
- javaserverx64
- javaclientex64
- javanodex86
- liblinux.so
- java.h
- open.h
- mpt86.h
- sqlsearch.php
- indexq.php
- mt64.so
- certbot.h
- cert.h
- certbotx64
- certbotx86
- javautils
- search.so
Credential Exfil Domains
- *.x3206.caixa.cx
- *.dev21.bancodobrasil.dev
| IP | Country |
|---|---|
| 109.202.202.202 | Switzerland |
| 91.189.91.43 | United Kingdom |
| 91.189.91.42 | United Kingdom |
Source: https://www.intezer.com/blog/research/new-linux-threat-symbiote/
htps://securityaffairs.co/wordpress/132113/malware/symbiote-linux-malware.html
https://www.joesandbox.com/analysis/1010003#iocs