In the lockdown days, we all had online classes and would keep our siblings in front of the laptop, and the same thing happens in the computer security world. Attackers impersonate legitimate users and systems to gain the trust of third parties. Hiding their own identity and carrying out malicious acts is not a new attack technique.
A masquerade attack is one in which the attacker poses as an authorized user of a system to gain access to it or greater privileges than they are authorized for. A masquerade can be attempted by using stolen login IDs and passwords, finding security holes in software, or bypassing the authentication mechanism.
Weak authentication makes it much easier for an attacker to gain access, causing it one of the easiest points of entry for a masquerade. Once authorized, the attacker may have full access to the organization’s important data and may be able to modify and delete software and data, as well as make changes to network configuration and routing information (depending on the privilege level they pretend to have).
In this blog, we are going to see what is Masquerade attack, a technique used to do masquerading, detection, and mitigation.
Also Read: Latest IOCs – Threat Actor URLs , IP’s & Malware Hashes
Masquerade attack – Definition:
Adversaries may try to manipulate features of their artifacts to appear legitimate or benign to users and/or security tools. Masquerading occurs when the name or location of a legitimate or malicious object is manipulated or abused to evade defenses and observation. This may include tampering with file metadata, duping users into misidentifying file types, and impersonating legitimate task or service names. This technique has been observed in several variations.
Mitre Tactics and Techniques:
Tactic: Defense Evasion
Technique: Masquerading (ID: T1036)
Sub Technique:
- Invalid Code Signature (T1036.001)
- Right-to-Left Override (T1036.002)
- Rename System Utilities (T1036.003)
- Masquerade Task or Service (T1036.004)
- Match Legitimate Name or Location (T1036.005)
- Space after Filename (T1036.006)
- Double File Extension (T1036.007)
Sub-Technique 1 – Invalid Code Signature (T1036.001):
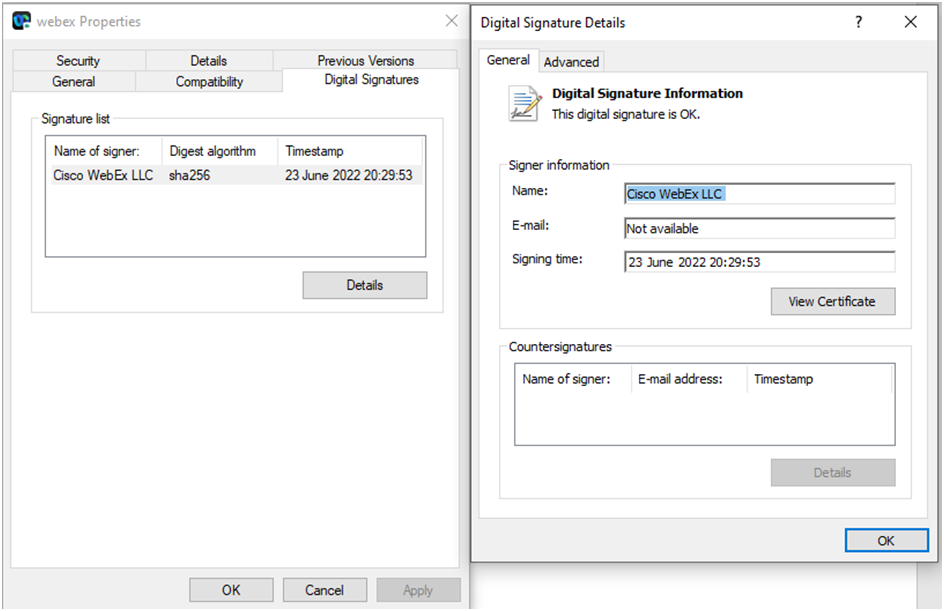
- Malicious actors may attempt to imitate features of valid code signatures to deceive a user, analyst, or tool. Code signing authenticates a binary from the developer and ensures that the binary has not been tampered with.
- Adversaries can use a signed program’s metadata and signature information as a template for an unsigned software system.
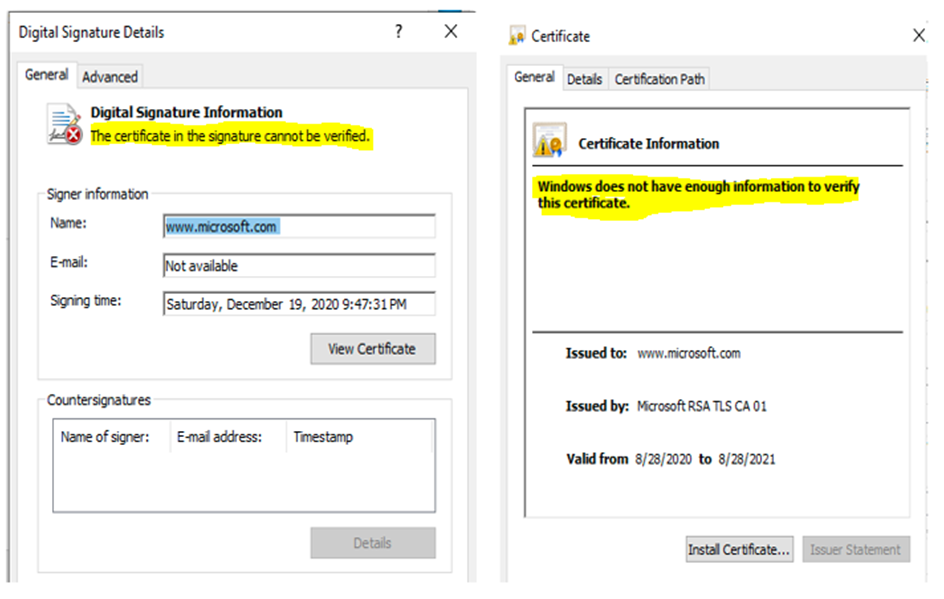
- Invalid code signatures will fail digital signature validation checks, but they may appear more legitimate to users, and security tools may handle these files inaccurately.
Example:
Spoofed Digital signatures can bypass AV and pass undetected by analysts because they provide a level of authenticity. Of course, we have the option to install this certificate with proper permissions, but I’m just trying to demonstrate how this “Signature” can provide some level of authenticity because it is Signed by Microsoft, and of course, a solid analyst can see that this has been valid from a recent date. We can create this digitally signed binary using the CarbonCopy tool. Fine the below 2 screenshots with and without a Digital Signature.
Picture 1 – With signature:
Picture 2 – Without Signature:
Sub-Technique 2 – Right-to-Left Override (T1036.002):
A right-to-left override (RTLO) attack exploits user trust in files/images by changing the file extension to a “.exe” executable file. An RTLO attack is a sophisticated phishing technique that fools users into thinking they are opening a harmless file when, in fact, they are opening a malicious executable. It’s one of several methods ransomware authors use to get their malware on corporate computers.
Also Read: New Aggah Campaign returns with new TTPS – Detection & Response
Attackers will use the character “(U+202E)” in the file name to dupe a user into running what they believe is a harmless file type but is executable code. RTLO can also be used in the Windows Registry, where regedit.exe displays reverse characters by default but the command-line tool reg.exe does not.
Example:
If the actual file name is “mytextfile.txt” and after inserting the RTLO character (mytext[U+202e]file.txt), it looks like “mytexttxt.elif”. All letters displayed after the Unicode character are reversed, and the name changes.
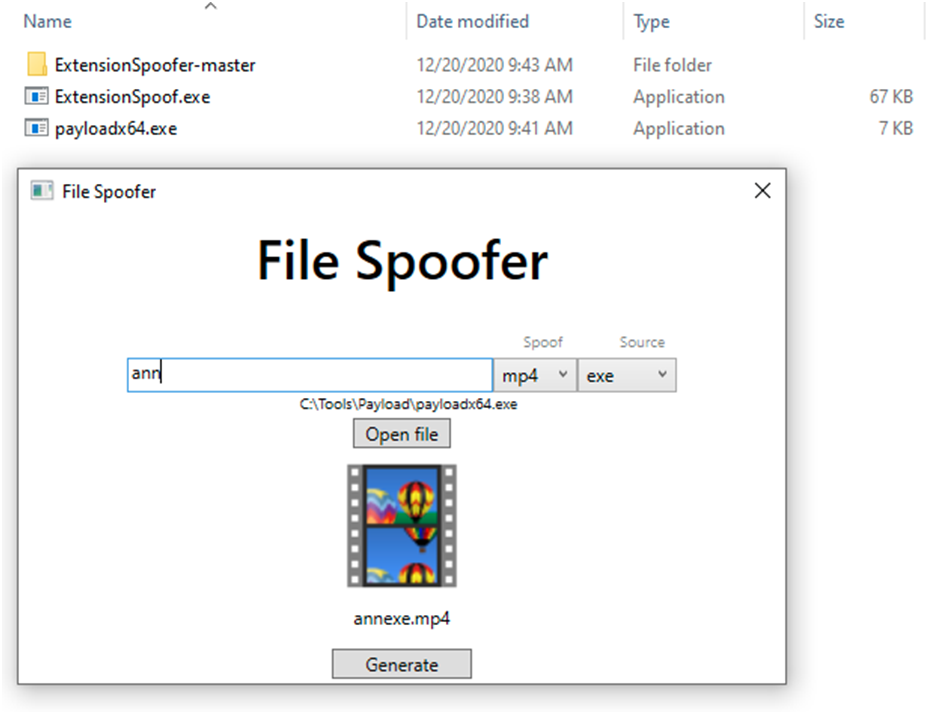
Using henriksb’s Extension Spoofer tool(https://github.com/henriksb), attackers can hide the original identity of the file. It spoofs extensions with the RTLO and disguises the binary by changing its icon.
Sub-Technique 3 – Rename System Utilities (T1036.003):
Malicious actors rename legitimate system utilities to bypass security mechanisms. Security monitoring and control mechanisms for system utilities may be in place for adversaries to exploit. It may be possible to bypass those security mechanisms by renaming the utility prior to use. Another scenario is when a legitimate utility is copied or moved to a different directory and renamed in order to avoid detections based on system utilities running from non-standard paths.
Also Read: Anatomy Of An Advanced Persistent Threat Group
Example:
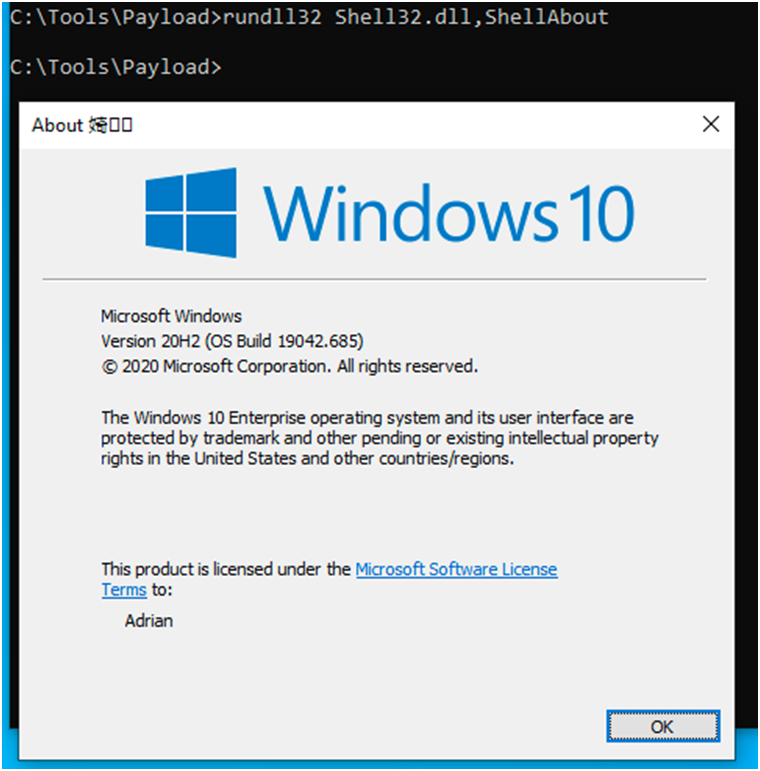
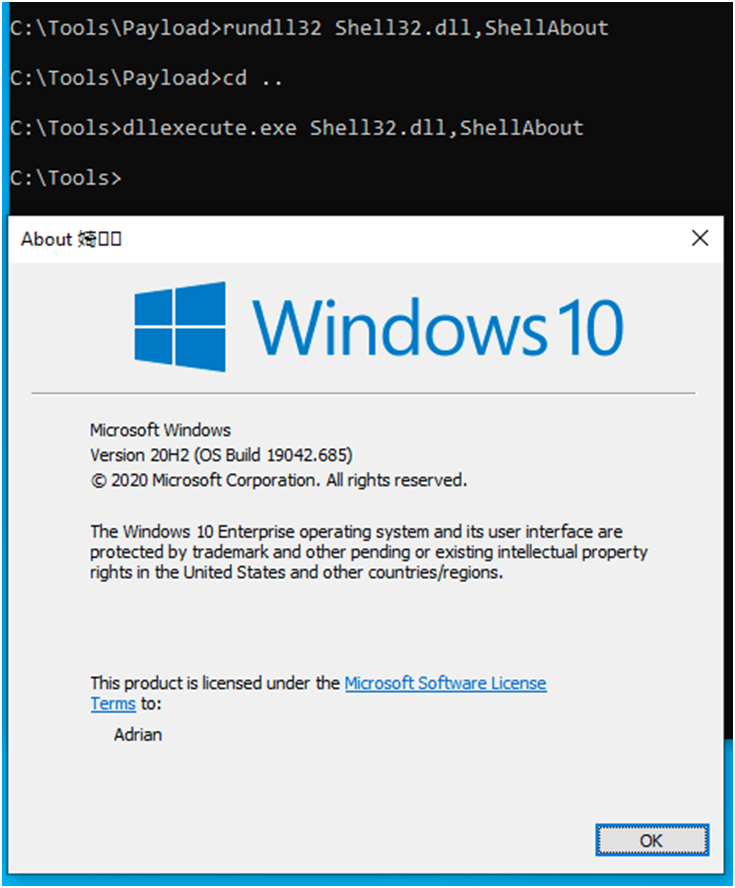
This technique will take legitimate system utilities and simply rename them; sometimes logging or IDS are looking for specific strings that will prevent execution; however, what if instead of calling runddl32, we call “dllexecute”; this would be rundll32 but just renamed. The execution and functionality will remain unchanged, but it will avoid defenses because the string is no longer rundll32.
Renaming utilities can sometimes be enough to get around security. In previous research, it appears that renaming your payload to MSBuild was enough to prevent Defender from scanning your payload.
Below are the two different syntaxes, but the same outcome. Rundll32 has only been renamed, but its functionality has not changed.
We’ve already gone over the attack and the three masquerading techniques. In the following blog, we will continue with the rest techniques. Stay tuned!!