DeepBlueCLI is an open-source framework that automatically parses Windows event logs, either on Windows (PowerShell version) or now on ELK (Elasticsearch).
Working with DeepBlueCLI
DeepBluCLI is available in Github. PowerShell must be run as Administrator and Please read the Set-ExecutionPolicy.
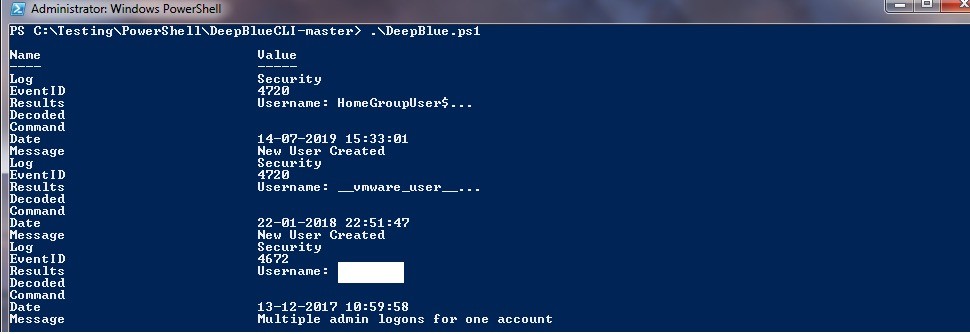
For a simple Process local Windows security event log:
| .\DeepBlue.ps1 |
You will definitely receive a “running scripts is disabled on this system” error.
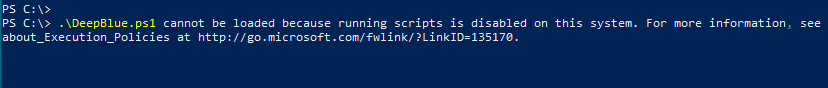
Please run the below commands: For more details, Check Set-Execution Policy Readme
| Set-ExecutionPolicy RemoteSigned – This will warn you every time you run a ps1 script. |
| Set-ExecutionPolicy Bypass – This command will bypass Set-Execution entirely. |
| Set-ExecutionPolicy Bypass – This command will help you with more options. |
Some of the Sample Events with their Commands:
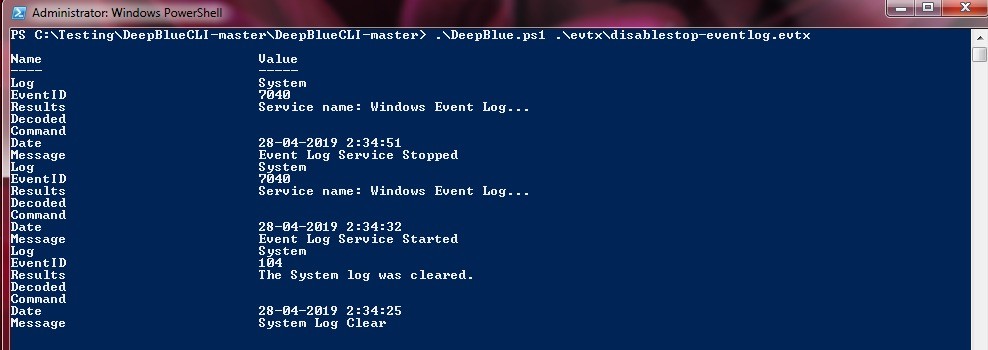
Event log manipulation:
| .\DeepBlue.ps1 .\evtx\disablestop-eventlog.evtx |
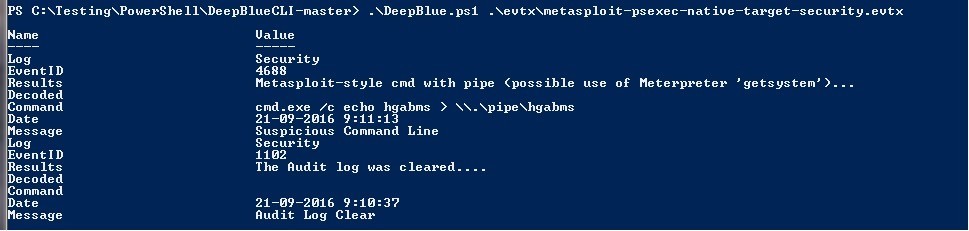
Metasploit native target (security):
.\DeepBlue.ps1 .\evtx\metasploit-psexec-native-target-security.evtx |
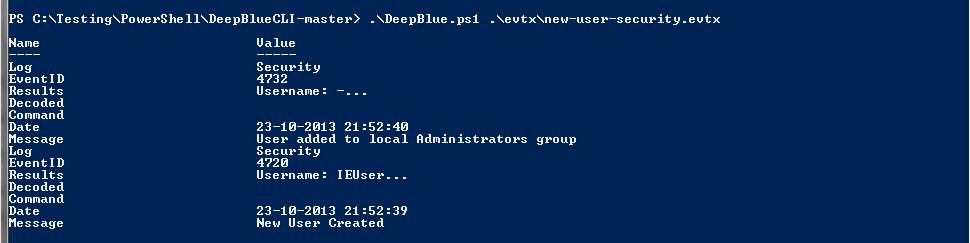
New user creation:
.\DeepBlue.ps1 .\evtx\new-user-security.evtx |
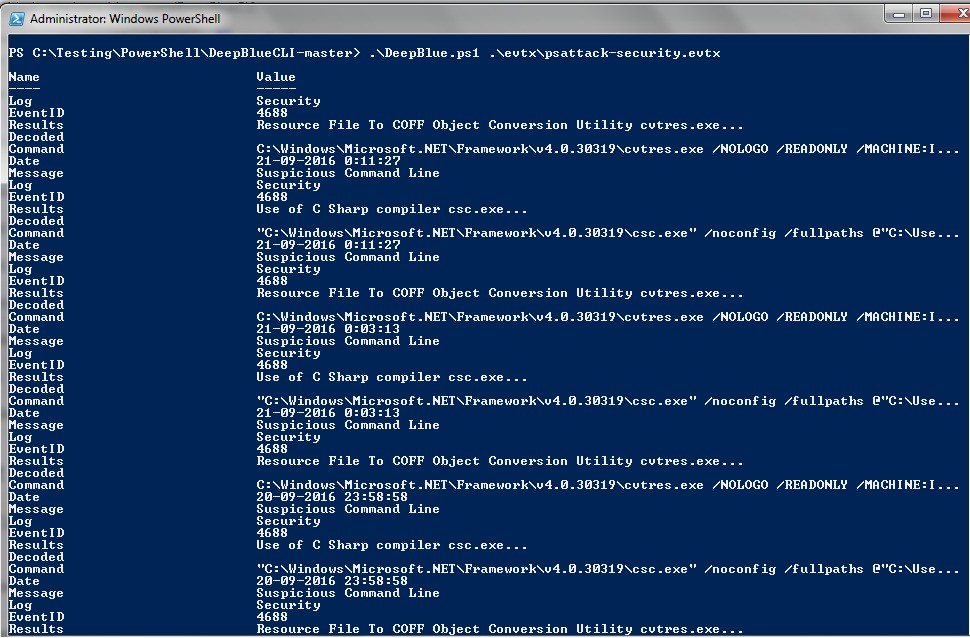
PSAttack:
.\DeepBlue.ps1 .\evtx\psattack-security.evtx |
Output:
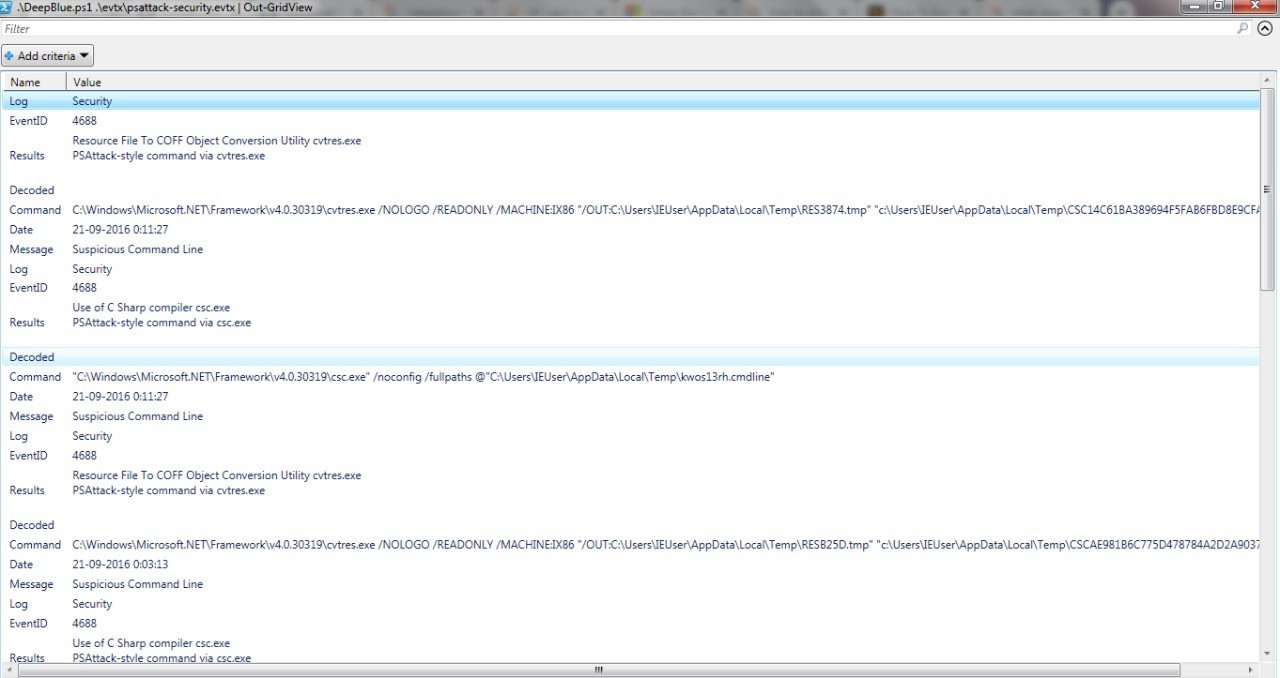
DeepBlueCLI outputs in PowerShell objects, allowing a variety of output methods and types, including JSON, HTML, CSV, etc.
One of the familiar/easy formats is a GridView:
.\DeepBlue.ps1 .\evtx\psattack-security.evtx | Out-GridView |
Windows Event Logs processed:
- Windows Security.
- Windows System.
- Windows Application.
- Windows PowerShell.
Sysmon.
Also Read : Soc Interview Questions and Answers – CYBER SECURITY ANALYST
Command Line Logs processed:
See Logging setup section below for how to configure these logs:
- Windows Security event ID 4688.
- Windows PowerShell event IDs 4103 and 4104.
- Sysmon event ID 1.
Detected Events:
Suspicious account behavior:
• User creation.
• User added to local/global/universal groups.
• Password guessing (multiple logon failures, one account).
• Password spraying via failed logon (multiple logon failures, multiple accounts).
• Password spraying via explicit credentials.
• Bloodhound (admin privileges assigned to the same account with multiple Security IDs).
Command line/Sysmon/PowerShell auditing:
• Long command lines.
• Regex searches.
• Obfuscated commands.
• PowerShell launched via WMIC or PsExec.
• PowerShell Net.WebClient Downloadstring.
• Compressed/Base64 encoded commands (with automatic decompression/decoding).
• Unsigned EXEs or DLLs.
Also Read : Latest IOCs – Threat Actor URLs , IP’s & Malware Hashes
Service auditing:
• Suspicious service creation.
• Service creation errors.
• Stopping/starting the Windows Event Log service (potential event log manipulation).
Mimikatz:
• lsadump::sam
• EMET & Applocker Blocks.
Demo:
Other Events with Commands:
| Event | Command |
| Event log manipulation | .\DeepBlue.ps1 .\evtx\disablestop-eventlog.evtx |
| Metasploit native target (security) | .\DeepBlue.ps1 .\evtx\metasploit-psexec-native-target-security.evtx |
| Metasploit native target (system) | .\DeepBlue.ps1 .\evtx\metasploit-psexec-native-target-system.evtx |
| Metasploit PowerShell target (security) | .\DeepBlue.ps1 .\evtx\metasploit-psexec-powershell-target-security.evtx |
| Metasploit PowerShell target (system) | .\DeepBlue.ps1 .\evtx\metasploit-psexec-powershell-target-system.evtx |
Mimikatz lsadump::sam | .\DeepBlue.ps1 .\evtx\mimikatz-privesc-hashdump.evtx |
| New user creation | .\DeepBlue.ps1 .\evtx\new-user-security.evtx |
| Obfuscation (encoding) | .\DeepBlue.ps1 .\evtx\Powershell-Invoke-Obfuscation-encoding-menu.evtx |
| Obfuscation (string) | .\DeepBlue.ps1 .\evtx\Powershell-Invoke-Obfuscation-string-menu.evtx |
| Password guessing | .\DeepBlue.ps1 .\evtx\smb-password-guessing-security.evtx |
| Password spraying | .\DeepBlue.ps1 .\evtx\password-spray.evtx |
| PowerSploit (security) | .\DeepBlue.ps1 .\evtx\powersploit-security.evtx |
| PowerSploit (system) | .\DeepBlue.ps1 .\evtx\powersploit-system.evtx |
| PSAttack | .\DeepBlue.ps1 .\evtx\psattack-security.evtx |
| User added to administrator group | .\DeepBlue.ps1 .\evtx\new-user-security.evtx |
Output Formats:
| Output Type | Syntax |
| CSV | .\DeepBlue.ps1 .\evtx\psattack-security.evtx | ConvertTo-Csv |
| Format list (default) | .\DeepBlue.ps1 .\evtx\psattack-security.evtx | Format-List |
| Format table | .\DeepBlue.ps1 .\evtx\psattack-security.evtx | Format-Table |
| GridView | .\DeepBlue.ps1 .\evtx\psattack-security.evtx | Out-GridView |
| HTML | .\DeepBlue.ps1 .\evtx\psattack-security.evtx | ConvertTo-Html |
| JSON | .\DeepBlue.ps1 .\evtx\psattack-security.evtx | ConvertTo-Json |
| XML | .\DeepBlue.ps1 .\evtx\psattack-security.evtx | ConvertTo-Xml |



































