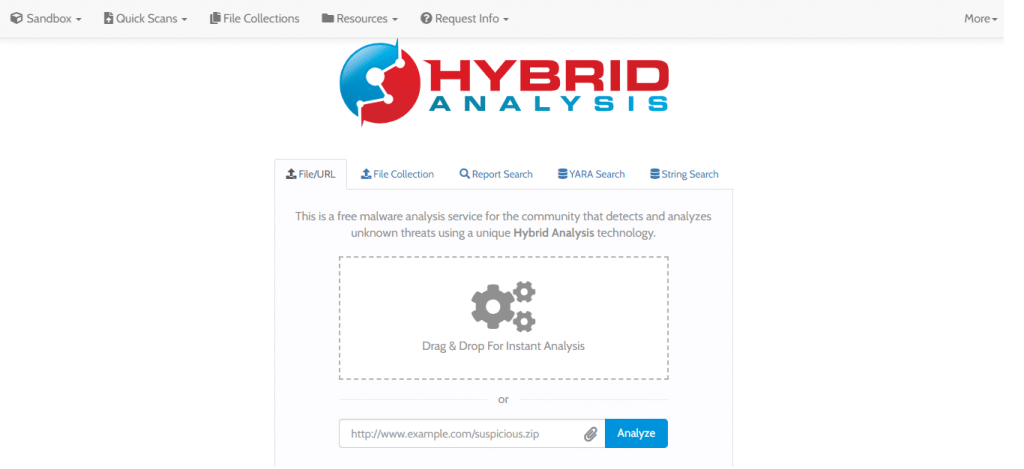
What is Hybrid Analysis?
Hybrid Analysis is a platform for analyzing malware (in-depth static and dynamic analysis) with the Falcon Sandbox and Hybrid Analysis technology. It combines runtime data with extensive static analysis of memory dumps to extract annotated disassembly listings and deduct additional IOCs (strings/API call chains). This unique feature allows extraction of behavior indicators regardless of execution and helps detect unknown threats even of the most evasive malware. All data extracted from the Hybrid Analysis engine is processed automatically and integrated into the Falcon Sandbox reports.
What is Falcon Sandbox?
Falcon Sandbox is a high-end malware analysis framework with a very agile architecture. It can be implemented as a large-scale system processing hundred of thousands of files automatically (utilizing e.g. the simple REST API) or as a web service for incident response, forensics, and/or as an enterprise self-service portal.
Due to its simple interface and numerous integration capabilities with other technology providers, it seamlessly enriches a SOCs incident response workflow and security stack. Falcon Sandbox is currently in use by SOCs, CERTs, DFIR teams, IT-security forensic labs, researchers, and threat intelligence service providers all around the world. Multiple S&P 100, Fortune 500 and U.S. government agencies are using Falcon Sandbox and enjoying it every day. Please take a look at the Falcon Sandbox product page for more information.
It is possible to analyze a group of files, but in order to do so there are some additional requirements:
• Archive format must be ZIP.
• Archive need to contain start file.
• Archive needs to have all files (directories are not supported) in the same location as the start file.
In order to know which file needs to be run, an init.properties file need to be included. This file needs to include the following syntax: startFile=[startFileName]
For example: startFile=sample.exe
This free Malware analysis service comes with convenient “Quick Scan” endpoints that perform CrowdStrike Falcon Static Analysis (ML) and e.g. Metadefender AV scans rapidly. To do bulk scans, utilize the ‘scan_file’ CLI of the VxAPI Python API connector or utilize the Quick Scan endpoints directly.
For easier access, Please find the online Malware Sandbox in our website.

Supporting Platforms:
Currently, it supports hybrid (static and runtime) analysis on Windows XP, Vista, Windows 7/8, 10, and extensive static analysis for Android APK files. Also, it supports VirtualBox and VMWare solutions (e.g. ESXi).
Falcon Sandbox offers a wide range of integrations including:
• VirusTotal and OPSWAT Metadefender (online and on-site)
• SIEM systems (e.g. HP ArcSight)
• NSRL (Whitelist)
• Thug honeyclient (e.g. URL exploit analysis)
• Suricata (ETOpen/ETPro rules)
• TOR (avoid e.g. external IP fingerprinting)
• Phantom
File Limitations:
You can upload archives in one of the following formats with/without a password: ace, arj, 7z, bzip2, gzip2, iso, rar, rev, tar, Wim, xz, and zip. If you use a password, only the typical ‘infected’ password is accepted.
Additional limits to archives:
• Maximum number of files: 20
• Maximum nested level: 1
• Maximum size of an archive: 100MB
• Maximum size of the single file in the archive: 100MB
API for the web interface:
The API is very extensive and supports a wide range of operations, including, but not limited to: single/bulk file and URL submissions, advanced search capabilities, report data retrieval and data erasure (based on privileges). All registered users can generate a restricted free Public API key. For more information, please visit our Public API information page
Advanced search options:
There is a variety of advanced search queries. You can search for a virus family name, find all reports that contacted a specific IP address, domain, URL, have a specific file type, fuzzy hash, #hashtag, shared artifact, and so on.
Here are selected examples of some advanced search operators:
• host:95.181.53.78
• port:3448
• domain:checkip.dyndns.org
• indicatorid:network-6 (Show all reports matching ‘Contacts Random Domain Names’)
• filetype:jar
• filetype_tag:hwp
• url:google
• similar-to:hash
• authentihash:hash
• tag:teslacrypt
What is a behavior indicator?
A behavior indicator is a small script file that registers itself for a specific data type or event and abstracts the input to a specific behavior, such as when a malware adds an entry to an autostart registry pathway, changes firewall settings, injects into another process or sends data on unusual ports. Behavior indicators are classified as either “malicious”, “suspicious” or simply “informative”. As each indicator includes information about the data that made it trigger, it becomes easier to understand the functionality of the analyzed malware/software in-depth and find entry points for deeper analysis.
Kinds of Data for Analysis:
Behavior indicators can trigger on a multitude of data types or events. Some of them include registry accesses, process memory strings, API calls, created mutants/files, network traffic, injected processes, disassembly instructions, and a lot more.
Currently, the full version comes with multiple hundred generic behavior indicators and thousands of YARA rules ready to use. Part of the daily work of our development team is to add new behavior indicators. As we come across interesting samples a lot, the number of behavior indicators is constantly growing.
Decrypted SSL traffic is included for Windows analysis on a per-host basis in the “Network Analysis” section of the report (see “Show SSL” buttons and subsequent model).
Conclusion:
Many Researchers have used static, dynamic, and hybrid processes to detect malware and malicious activities. Falcon Sandbox has a powerful and simple API that can be used to submit files/URLs for analysis, we can able to pull the report, and also perform advanced search queries. This API is open and free to the entire IT-security community. Please make use of this tool for malware research.



































