Experts warn that operators behind the Qakbot malware operation are improving their attack chain in an attempt to avoid detection. Qakbot, also known as QBot, QuackBot, and Pinkslipbot, is an info-stealing malware that has been active since 2008. The malware spreads via malspam campaigns, it inserts replies in active email threads.
Also Read: Latest IOCs – Threat Actor URLs , IP’s & Malware Hashes
The threat continues to evolve implementing new attack vectors to evade detection, Zscaler Threatlabz researchers warn. The experts spotted a significant uptick in the spread of Qakbot malware over the past six months using several new techniques.
Most recently, threat actors have transformed their techniques to evade detection by using ZIP file extensions, enticing file names with common formats, and Excel (XLM) 4.0 to trick victims into downloading malicious attachments that install Qakbot.” reads the analysis published by Zscaler. “Other more subtle techniques are being deployed by threat actors to prevent automated detection and raise the odds that their attack will work, including obfuscating code, leveraging multiple URLs to deliver the payload, using unknown file extension names to deliver the payload, and altering the steps of the process by introducing new layers between initial compromise, delivery, and final execution.
The attacks observed by Zscaler employed malicious messages using ZIP archive file having embedded files such as Microsoft Office files, LNK, and Powershell.
Also Read: Threat Actors Use New Red-Teaming Tool BRc4 to Evade – Detection & Response
ThreatLabz reported that the attackers are using various different file names to disguise attachments designed to deliver Qakbot. Common file names used in the recent campaigns include a description, generated numbers, and dates (i.e. Compensation-1172258432-Feb-16.xlsb, Compliance-Report-1634724067-Mar-22.xlsb). The files also feature common keywords for finance and business operations the attempt to trick victims into believing that they are everyday business documents.
“Once the user clicks “Enable Content” to view the attachment, the macro is activated to look for a subroutine with a pre-defined function, in this case starting with auto_open777777. In the next step of the sequence, the URLDownloadToFile function is imported and called to download the malicious Qakbot Payload and drop it into the C:\ProgramData\ location on the victim’s machine with the filename .OCX which is actually Qakbot DLL.” continues the analysis. “Then WinAPI EXEC from Excel4Macro directly executes the malicious payload or loads the payload using regsvr32.exe.”
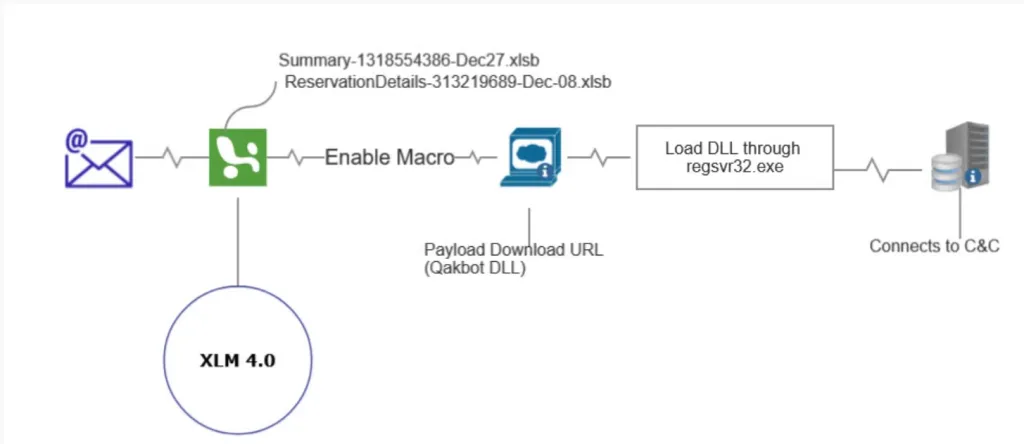
The experts also observed the use of PowerShell to download the malicious code and a switch from regsvr32.exe to rundlll32.exe to load the malicious payload in the attempt to evade detection.
Also Read: Soc Interview Questions and Answers – CYBER SECURITY ANALYST
Zscaler researchers highlight the importance of the human factor for the success of these attacks, it recommends that organizations train users to properly manage attachments, avoiding opening attachments sent from untrusted or unknown sources. The experts also recommend users verify URLs in their browser address bar before entering credentials.
Indicator of Compromise:
[+] C2 IPs:
1.161.123.53
101.108.199.194
102.182.232.3
103.116.178.85
103.207.85.38
104.34.212.7
106.51.48.170
108.60.213.141
109.12.111.14
109.178.178.110
111.125.245.116
117.248.109.38:21
120.150.218.241
120.61.2.215
121.7.223.45
124.40.244.115
140.82.49.12
140.82.63.183
143.0.219.6
144.202.2.175
144.202.3.39
148.0.56.63
148.64.96.100
149.28.238.199
172.115.177.204
173.174.216.62
173.21.10.71
174.69.215.101
175.145.235.37
176.205.23.48
176.67.56.94
177.209.202.242
177.94.57.126
179.158.105.44
180.129.108.214
182.191.92.203
186.90.153.162
187.207.131.50
187.251.132.144
189.146.87.77
189.223.102.22
189.253.206.105
189.37.80.240
189.78.107.163
190.252.242.69
191.112.4.17
191.34.120.8
193.136.1.58
196.203.37.215
197.87.182.115
197.94.94.206
201.145.165.25
201.172.23.68
201.242.175.29
208.101.82.0
208.107.221.224
210.246.4.69
Indicators of Compromise
[+] Payload URLs:
anukulvivah.comnobeltech[.]com.pk
griffinsinternationalschool.intierrasdecuyo[.]com.ar
tajir[.]comdocumentostelsen[.]com
wrcopias[.]com.brls[.]com.co
dk-chic[.]combendhardwoodflooring[.]com
stalwartnv[.]comdelartico[.]com
newportresearchassociates[.]comjindalfabtex[.]com
softwarela.orgasesorescontables[.]com.py
segurabr[.]com.brrenty.biz
hams.psalrabbat[.]com
glistenworld[.]comsonalifecare[.]com
act4dem.netbrandxo.in
stuttgartmed[.]comgmstrust.in
act4dem.netglistenworld[.]com
ananastours[.]comhostingdeguatemala[.]com
gmsss45c[.]comasiatrendsmfg[.]com
facturamorelos[.]comjnpowerbatteries[.]com
minimean[.]com1031taxfreexchange[.]com
pbxebike[.]comhigradeautoparts[.]com
parkbrightworldwideltd[.]comams.org.co
baalajiinfotechs[.]commomoverslegypte[.]com
recetasparaelalmapanama[.]comghssarangpur.org
wecarepetz[.]com.brbrothersasian[.]com
knapppizzabk[.]comwecarepetz[.]com.br
jeovajirelocacao[.]com.br7n7u.tk
amdpl.indabontechnologies.co.ke
bouncehouserentalmiami.netmahasewanavimumbai[.]com
hotelsinshillong.inbrothersasian[.]com
tamiltechhints[.]comitaw-int[.]com
tvtopcultura[.]com.brmadarasapattinam[.]com
desue.mxautocadbeginner[.]com
antwerpdiamond.netmarciomazeu.dev.br
ifongeek[.]comtunaranjadigital[.]com
avaniamore[.]comthecoursecreators[.]com
thecoursecreators[.]comdrishyamopticals[.]com
thewebinarchallenge[.]comiammyprioritylive[.]com
erekha.invegascraftbeertour[.]com
rommify.orgpbsl[.]com.gh
sathyaunarsabha.orgcourtalamarivuthirukovil.org
pbsl[.]com.ghapk.hap.in
outsourcingmr[.]comofferlele[.]com
courtalamarivuthirukovil.orgelchurritorojas[.]com
apk.hap.inklicc.co.tz
jinglebells.ngthebrarscafe[.]com
bigtv3d.inretroexcavaciones[.]com
aimwithnidhi.invizionsconsulting[.]com
gaurenz[.]comamarelogema[.]com.br
wiredcampus.inretroexcavaciones[.]com
elchurritorojas[.]comglobalwomenssummit2020[.]com
byonyks[.]comwfgproduction[.]com
wfgproduction[.]comciit.edu.ph
reachprofits[.]comcreativecanvas.co.in
vegascraftbeertour[.]comnightsclub[.]com
assistenciatecnicaembh24h[.]com.brtheinfluencersummit2021[.]com
grupoumbrella[.]com.brbjfibra[.]com
fra[.]com.arthewebinarstore[.]com
writeright.inaaafilador.eu
wlrinformatica[.]com.brminahventures[.]com
alternativecareers.inwvquali[.]com.br
aaafilador.eueventbriteclone.xyz
policepublicpress.inmarcofoods.in
longwood-pestcontrol[.]comlifecraze.in
viasalud.mxecsshipping[.]com
misteriosdeldesierto.pelgfcontabilidade[.]com.br
mariebeeacademy[.]commuthumobiles[.]com
teamone[.]com.satechmahesh.in
wiredcampus.inteamone[.]com.sa
furnitureion[.]comekofootball[.]com
comunidadecristaresgate[.]com.bryqsigo[.]com
mysuccesspoint.inkriworld.net
wiredcampus.intheinfluencerlaunch[.]com
mi24securetech[.]compalconsulting.net
attalian[.]comrudrafasteners[.]com
filmandtelevisionindia[.]comcloudberrie[.]com
brikomechanical[.]comideiasnopapel[.]com.br
neovation.sgatozinstrument[.]com
tecnobros8[.]comwalnut.ae
brikomechanical[.]comleaoagronegocios[.]com.br
sonhomirim[.]com.brwlrinformatica[.]com.br
wbbvet.ac.inboostabrain.in
narendesigns[.]comsla[.]com.ng
rstkd[.]com.brdelacumbrefm[.]com
leaoagronegocios[.]com.brdegreesdontmatter.in
strategicalliances.co.inlelokobranding.co.za
metrointl.netrajkotbusiness.in
titanhub.co.ukgrupothal[.]com.br
www.centerplastic[.]com.brpawnest[.]com
rightsupportmanagement.co.uksmiletours.net
leaseicemachine[.]comsegiaviamentos[.]com.br
virtualexpo.cactusfuturetech[.]comautovidriosrobin.anuncio-ads.cl
klearning.co.ukbestbuidan.mn
amicodelverde[.]comhunbuzz[.]com
prova.gaia.srlprodotti.curadelprato[.]com
prodotti.curadelprato[.]comdomenico[.]com.co
anukulvivah[.]comahmedabadpolicestories[.]com
ec.meticulux.netpent.meticulux.net
clerbypestcontrolllp.inorderingg.in
rylanderrichter[.]comtajir[.]com
searchgeo.org4md-uae[.]com
matjarialmomayz[.]comformularapida[.]com.br
carnesecaelpatron[.]com.mxbengallabourunion[.]com
alphanett[.]com.brragvision[.]com
secunets.co.keflameburger[.]com.mx
gph.lkabingdonhomes[.]com
agteacherscollege.ac.insis.edu.gh
impexlanka[.]comludoi[.]come.xyz
mufinacademy[.]com1031oilgasexchange[.]com
indexpublicidade[.]com.brhullriverinternationalltd[.]com
srgsdelhiwest[.]comproyectostam[.]com
waitthouseinc.orggomax.mv
ecotence.in.nettriplenetleaseproperty[.]com
brunocesar.meonlywebsitemaintenance[.]com
lbconsultores[.]com.cokindersaurus.in
guitarconnectionsg[.]comguestpostmachine[.]com
bagatiparamohiladegreecollege.edu.bdguitarconnectionsg[.]com
waitthouseinc.orgofferlele[.]com
cuddlethypet[.]comsrimanthexports[.]com
espetinhodotom[.]comluxiaafinishinglab[.]com
greyter[.]commoodle-on[.]com
niramayacare.inmakazadpharmacy[.]com
netleasesale[.]comnathanflax[.]com
erimaegypt[.]comclashminiwiki[.]com
topfivedubai[.]comskyorder.net
profitsbrewingnews[.]commotobi[.]com.bd
polistirolo.orgpalashinternationals[.]com
mayaconstructions.co.inmaexbrasil[.]com.br
mzdartworkservicesllc[.]comwalmondgroup[.]com
saffroneduworld[.]comlacremaynaty[.]com.mx
ifongeek[.]comgrowscaleandprofit[.]com
getishdonelive[.]cominfluencerlaunches[.]com
apk.hap.incalldekesha[.]com
vortex.cmspeakatiamp[.]com
thewebinarclinic[.]comthewebinarchecklist[.]com
sathyaunarsabha.orgoutsourcingmr[.]com
webdoweb[.]com.ngvortex.cm
future-vision[.]com.trbrunalipiani[.]com.br
ecotence.xyznimbus[.]com.qa
writeright.inlightnco.id
aidshivawareness.orgmetaunlimited.in
hearingaidbihar[.]combarcalifa[.]com.br
condominiosanalfonso.cltimelapse.ae
oladobeldavida[.]com.brmarcofoods.in
alternativecareers.inrsbnq[.]com
cobblux.pktafonego.org
chezmarblan[.]comcogitosoftware.co.in
devconstech[.]comcumipilek[.]com
daptec[.]com.brhydrical.mx
indiacodecafe[.]comecsshipping[.]com
skyorder.nettechmahesh.in
assimpresaroma.itcampandvillas[.]com
styleavail[.]comomtapovan[.]com
programandoavida[.]com.brindiacodecafe[.]com
bruno-music[.]comlaoaseanhospital.la
agbegypt[.]comcrimpwell.in
1031wiki[.]comstrategicalliances.co.in
nimbus[.]com.qavivanaweb[.]com.br
officeservicesjo.cfdinspiraanalytics.in
shareyourcake.orgprotocolostart[.]com
acertoinformatica[.]com.brinovex.in
devconstech[.]comdigizen.in
rajkotbusiness.indigizen.in
acertoinformatica[.]com.brrumbakids[.]com
boostabrain.incsnglobal.co
haskekudla[.]comkraushop[.]com
Mahalaxmibastralayanx.inchuckdukas[.]com
[+] Hashes
XLSB:
58F76FA1C0147D4142BFE543585B583F
4DFF0479A285DECA19BC48DFF2476123
D7C3ED4D29199F388CE93E567A3D45F9
3243D439F8B0B4A58478DFA34C3C42C7
396C770E50CBAD0D9779969361754D69
C2B1D2E90D4C468685084A65FFEE600E
LNK:
54A10B41A7B12233D0C9EACD11036954
E134136D442A5C16465D9D7E8AFB5EBE
7D0083DB5FA7DE50E620844D34C89EFC
C2663FCCB541E8B5DAA390B76731CEDE
Qakbot:
529FB9186FA6E45FD4B7D2798C7C553C
Detection & Response:
Splunk:
source="WinEventLog:*" AND ((Image="*\\cmd.exe") AND CommandLine="*curl.exe*" AND CommandLine="*ping*" AND CommandLine="*regsvr32.exe*" AND CommandLine="*localhost*" AND CommandLine="*regsvr32*" AND CommandLine="*.pos*" AND Image="*\\powershell.exe" AND CommandLine="*-NoExit*" AND CommandLine="*rundll32.exe*" AND CommandLine="*.dll*" AND CommandLine="*-OutFile*" AND CommandLine="*https:*" AND CommandLine="*Uri*" AND CommandLine="*Start-Process*" AND TargetFilename="*\\AppData\\Local\*\*.dll*")Qradar:
SELECT UTF8(payload) from events where LOGSOURCETYPENAME(devicetype)='Microsoft Windows Security Event Log' and ("Image" ilike '%\cmd.exe') and "Process CommandLine" ilike '%curl.exe%' and "Process CommandLine" ilike '%ping%' and "Process CommandLine" ilike '%regsvr32.exe%' and "Process CommandLine" ilike '%localhost%' and "Process CommandLine" ilike '%regsvr32%' and "Process CommandLine" ilike '%.pos%' and "Image" ilike '%\powershell.exe' and "Process CommandLine" ilike '%-NoExit%' and "Process CommandLine" ilike '%rundll32.exe%' and "Process CommandLine" ilike '%.dll%' and "Process CommandLine" ilike '%-OutFile%' and "Process CommandLine" ilike '%https:%' and "Process CommandLine" ilike '%Uri%' and "Process CommandLine" ilike '%Start-Process%' and UTF8(payload) ILIKE '%\AppData\Local\%\%.dll%'Elastic Query:
(process.executable:*\\cmd.exe AND process.command_line:*curl.exe* AND process.command_line:*ping* AND process.command_line:*regsvr32.exe* AND process.command_line:*localhost* AND process.command_line:*regsvr32* AND process.command_line:*.pos* AND process.executable:*\\powershell.exe AND process.command_line:*\-NoExit* AND process.command_line:*rundll32.exe* AND process.command_line:*.dll* AND process.command_line:*\-OutFile* AND process.command_line:*https\:* AND process.command_line:*Uri* AND process.command_line:*Start\-Process* AND file.path:*\\AppData\\Local\*\*.dll*)Arcsight:
(deviceVendor = "Microsoft" AND deviceProduct = "Microsoft Windows" AND externalId = "4688" AND ((deviceProcessName CONTAINS "*\\cmd.exe" OR destinationProcessName CONTAINS "*\\cmd.exe" OR sourceProcessName CONTAINS "*\\cmd.exe")) AND (((deviceCustomString4 CONTAINS "curl.exe" OR destinationServiceName CONTAINS "curl.exe")) AND ((deviceCustomString4 CONTAINS "ping" OR destinationServiceName CONTAINS "ping")) AND ((deviceCustomString4 CONTAINS "regsvr32.exe" OR destinationServiceName CONTAINS "regsvr32.exe")) AND ((deviceCustomString4 CONTAINS "localhost" OR destinationServiceName CONTAINS "localhost")) AND ((deviceCustomString4 CONTAINS "regsvr32" OR destinationServiceName CONTAINS "regsvr32")) AND ((deviceCustomString4 CONTAINS ".pos" OR destinationServiceName CONTAINS ".pos"))) AND ((deviceProcessName ENDSWITH "\\powershell.exe" OR destinationProcessName ENDSWITH "\\powershell.exe" OR sourceProcessName ENDSWITH "\\powershell.exe")) AND (((deviceCustomString4 CONTAINS "-NoExit" OR destinationServiceName CONTAINS "-NoExit")) AND ((deviceCustomString4 CONTAINS "rundll32.exe" OR destinationServiceName CONTAINS "rundll32.exe")) AND ((deviceCustomString4 CONTAINS ".dll" OR destinationServiceName CONTAINS ".dll")) AND ((deviceCustomString4 CONTAINS "-OutFile" OR destinationServiceName CONTAINS "-OutFile")) AND ((deviceCustomString4 CONTAINS "regsvr32.exe" OR destinationServiceName CONTAINS "regsvr32.exe")) AND ((deviceCustomString4 CONTAINS "https:" OR destinationServiceName CONTAINS "https:")) AND ((deviceCustomString4 CONTAINS "Uri" OR destinationServiceName CONTAINS "Uri")) AND ((deviceCustomString4 CONTAINS "Start-Process" OR destinationServiceName CONTAINS "Start-Process"))) AND filePath CONTAINS "\\AppData\\Local\\*\\*.dll")CarbonBlack:
(process_name:*\\cmd.exe AND process_cmdline:*curl.exe* AND process_cmdline:*ping* AND process_cmdline:*regsvr32.exe* AND process_cmdline:*localhost* AND process_cmdline:*regsvr32* AND process_cmdline:*.pos* AND process_name:*\\powershell.exe AND process_cmdline:*\-NoExit* AND process_cmdline:*rundll32.exe* AND process_cmdline:*.dll* AND process_cmdline:*\-OutFile* AND process_cmdline:*https\:* AND process_cmdline:*Uri* AND process_cmdline:*Start\-Process* AND filemod_name:*\\AppData\\Local\*\*.dll*)Crowdstike:
(((ImageFileName="*\\cmd.exe") AND (CommandHistory="*curl.exe*" OR CommandLine="*curl.exe*") AND (CommandHistory="*ping*" OR CommandLine="*ping*") AND (CommandHistory="*regsvr32.exe*" OR CommandLine="*regsvr32.exe*") AND (CommandHistory="*localhost*" OR CommandLine="*localhost*") AND (CommandHistory="*regsvr32*" OR CommandLine="*regsvr32*") AND (CommandHistory="*.pos*" OR CommandLine="*.pos*")) AND (ImageFileName="*\\powershell.exe" AND (CommandHistory="*-NoExit*" OR CommandLine="*-NoExit*") AND (CommandHistory="*rundll32.exe*" OR CommandLine="*rundll32.exe*") AND (CommandHistory="*.dll*" OR CommandLine="*.dll*") AND (CommandHistory="*-OutFile*" OR CommandLine="*-OutFile*") AND (CommandHistory="*regsvr32.exe*" OR CommandLine="*regsvr32.exe*") AND (CommandHistory="*https:*" OR CommandLine="*https:*") AND (CommandHistory="*Uri*" OR CommandLine="*Uri*") AND (CommandHistory="*Start-Process*" OR CommandLine="*Start-Process*")) AND (TargetFileName="*\\AppData\\Local\*\*.dll*" OR TemporaryFileName="*\\AppData\\Local\*\*.dll*"))GrayLog:
(Image.keyword:*\\cmd.exe AND CommandLine.keyword:*curl.exe* AND CommandLine.keyword:*ping* AND CommandLine.keyword:*regsvr32.exe* AND CommandLine.keyword:*localhost* AND CommandLine.keyword:*regsvr32* AND CommandLine.keyword:*.pos* AND Image.keyword:*\\powershell.exe AND CommandLine.keyword:*\-NoExit* AND CommandLine.keyword:*rundll32.exe* AND CommandLine.keyword:*.dll* AND CommandLine.keyword:*\-OutFile* AND CommandLine.keyword:*https\:* AND CommandLine.keyword:*Uri* AND CommandLine.keyword:*Start\-Process* AND TargetFilename.keyword:*\\AppData\\Local\*\*.dll*)Logpoint:
(Image IN "*\\cmd.exe" CommandLine="*curl.exe*" CommandLine="*ping*" CommandLine="*regsvr32.exe*" CommandLine="*localhost*" CommandLine="*regsvr32*" CommandLine="*.pos*" Image="*\\powershell.exe" CommandLine="*-NoExit*" CommandLine="*rundll32.exe*" CommandLine="*.dll*" CommandLine="*-OutFile*" CommandLine="*https:*" CommandLine="*Uri*" CommandLine="*Start-Process*" TargetFilename="*\\AppData\\Local\*\*.dll*")Microsoft Defender:
DeviceProcessEvents | where ((FolderPath endswith @"\cmd.exe") and ProcessCommandLine contains "curl.exe" and ProcessCommandLine contains "ping" and ProcessCommandLine contains "regsvr32.exe" and ProcessCommandLine contains "localhost" and ProcessCommandLine contains "regsvr32" and ProcessCommandLine contains ".pos" and FolderPath endswith @"\powershell.exe" and ProcessCommandLine contains "-NoExit" and ProcessCommandLine contains "rundll32.exe" and ProcessCommandLine contains ".dll" and ProcessCommandLine contains "-OutFile" and ProcessCommandLine contains "https:" and ProcessCommandLine contains "Uri" and ProcessCommandLine contains "Start-Process" and FolderPath matches regex @".*\\AppData\\Local\.*\.*\.dll.*")Microsoft Sentinel:
SecurityEvent | where EventID == 1 | where ((NewProcessName endswith @'\cmd.exe') and CommandLine contains 'curl.exe' and CommandLine contains 'ping' and CommandLine contains 'regsvr32.exe' and CommandLine contains 'localhost' and CommandLine contains 'regsvr32' and CommandLine contains '.pos' and NewProcessName endswith @'\powershell.exe' and CommandLine contains '-NoExit' and CommandLine contains 'rundll32.exe' and CommandLine contains '.dll' and CommandLine contains '-OutFile' and CommandLine contains 'https:' and CommandLine contains 'Uri' and CommandLine contains 'Start-Process' and TargetFilename matches regex '(?i).*\AppData\Local\.*\.*.dll.*')RSA Netwitness:
((Image contains '\cmd\.exe') && (CommandLine contains 'curl.exe') && (CommandLine contains 'ping') && (CommandLine contains 'regsvr32.exe') && (CommandLine contains 'localhost') && (CommandLine contains 'regsvr32') && (CommandLine contains '.pos') && (Image contains 'powershell.exe') && (CommandLine contains '-NoExit') && (CommandLine contains 'rundll32.exe') && (CommandLine contains '.dll') && (CommandLine contains '-OutFile') && (CommandLine contains 'https:') && (CommandLine contains 'Uri') && (CommandLine contains 'Start-Process') && (TargetFilename regex '.*\\AppData\\Local\.*\.*\.dll.*'))Sumologic:
(_sourceCategory=*windows* AND (Image = "*\cmd.exe") AND CommandLine="*curl.exe*" AND CommandLine="*ping*" AND CommandLine="*regsvr32.exe*" AND CommandLine="*localhost*" AND CommandLine="*regsvr32*" AND CommandLine="*.pos*" AND Image="*\powershell.exe" AND CommandLine="*-NoExit*" AND CommandLine="*rundll32.exe*" AND CommandLine="*.dll*" AND CommandLine="*-OutFile*" AND CommandLine="*https:*" AND CommandLine="*Uri*" AND CommandLine="*Start-Process*" AND ("\AppData\Local\" AND "\" AND ".dll"))Google Chronicle:
target.process.file.full_path = /.*\\cmd\.exe$/ and target.process.command_line = /.*curl\.exe.*/ and target.process.command_line = /.*ping.*/ and target.process.command_line = /.*regsvr32\.exe.*/ and target.process.command_line = /.*localhost.*/ and target.process.command_line = /.*regsvr32.*/ and target.process.command_line = /.*\.pos.*/ and target.process.file.full_path = /.*\\powershell\.exe$/ and target.process.command_line = /.*-NoExit.*/ and target.process.command_line = /.*rundll32\.exe.*/ and target.process.command_line = /.*\.dll.*/ and target.process.command_line = /.*-OutFile.*/ and target.process.command_line = /.*https:.*/ and target.process.command_line = /.*Uri.*/ and target.process.command_line = /.*Start-Process.*/ and target.file.full_path = /.*\\AppData\\Local\\.*\\.*\.dll.*/Source/Credits: hs://securityaffairs.co/wordpress/133191/malware/qakbot-continues-to-evolve.html
https://www.zscaler.com/blogs/security-research/rise-qakbot-attacks-traced-evolving-threat-techniques