DnsTwist is the tool that can be used to discover potential malicious domains targeting your organization. This helps incident responders and soc analysts to spend fewer times on the incident investigation, response and reporting.
How does it work?
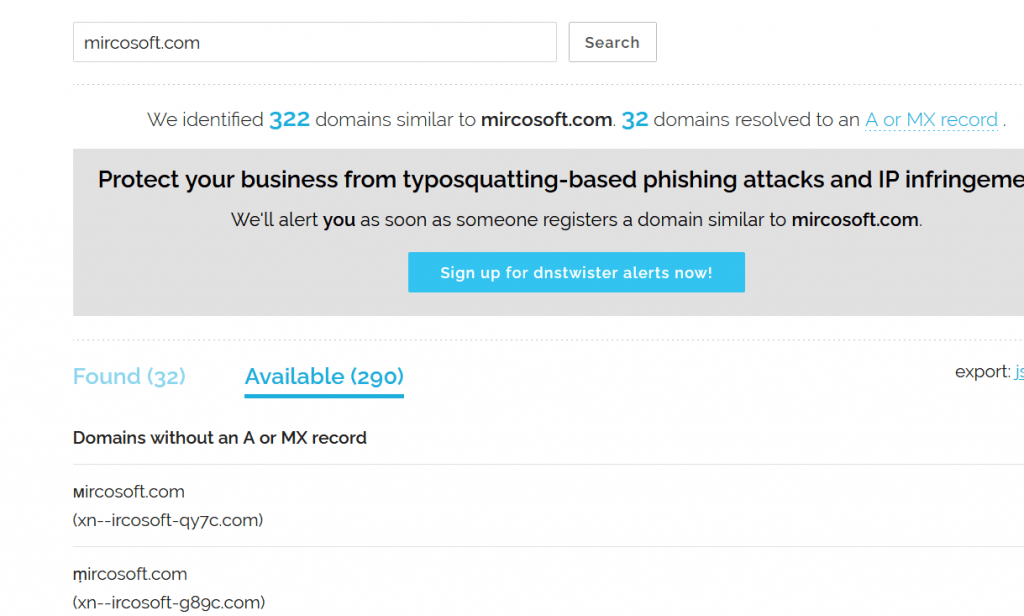
DnsTwist does a permutation scan on a large number of Phishing domains which is trying to mimic or impersonate your brand. It detects Typosquatting domains & Doppelganger domains. Once scans are getting completed, a List of other domains which is similar to your personal brand is shown on the results window. Results contain the Newly registered domains, IP addresses, Name servers, and Email servers.
Typosquatting domains
A Technique of registering a domain similar to the original domain. I.E, g00gle.com
Doppelganger domains
Missing dot “.” in the domain. I.E, mailg00gle.com
Getting Started
Try visiting the DNStwist online tool here
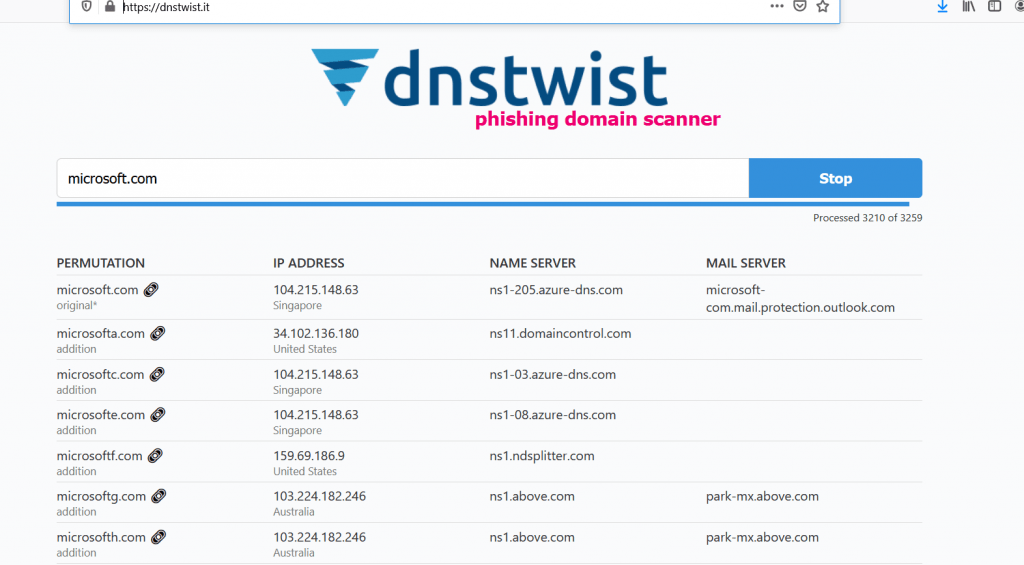
Do a Permutation scan on Dnstwist for the list of your customer’s brand and the vendors.
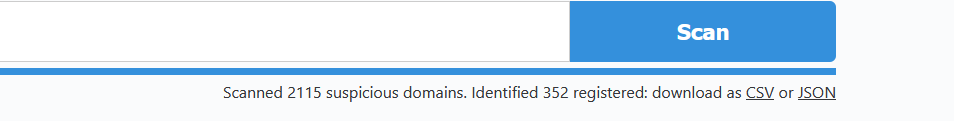
Export the suspicious domains as CSV or JSON formats. Exclude your customer’s and vendors’ legitimate domain from the downloaded CSV or JSON files.
Create a Watch list in your SIEM to monitor these domains, IP addresses, Name servers, and mail Servers. Take possible actions with the list of CSV’s as Block or Detect with Block with your security controls.
Also, Read Latest Cyber Security News – Hacker News !
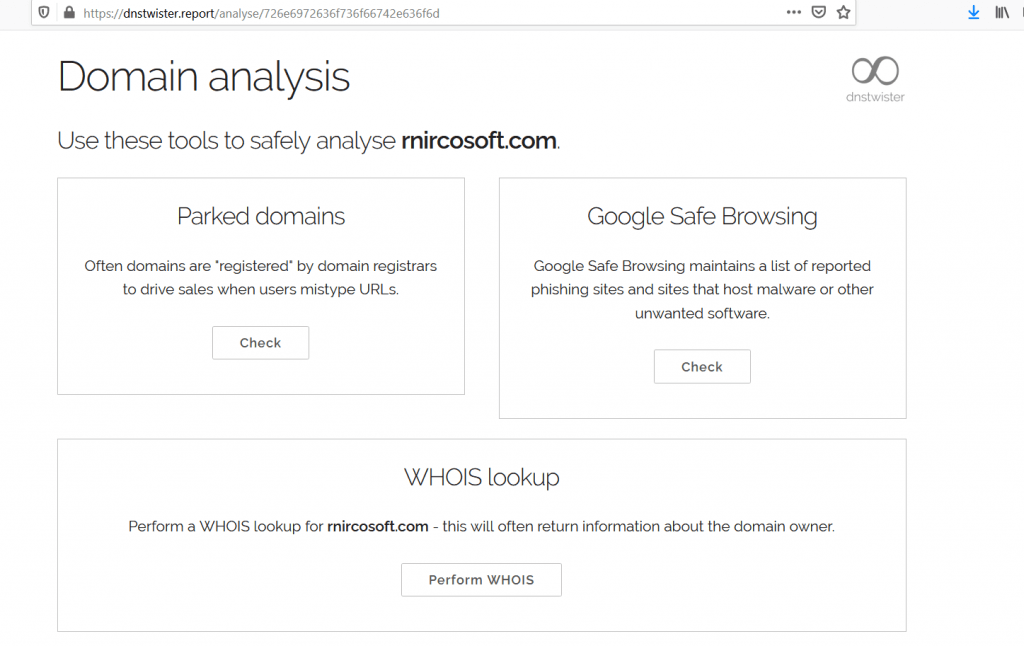
In addition use Dnstwister Reporter, this will help you get the Whois Lookup, Google safe browsing, and Parked domains lookups for the suspicious domains.
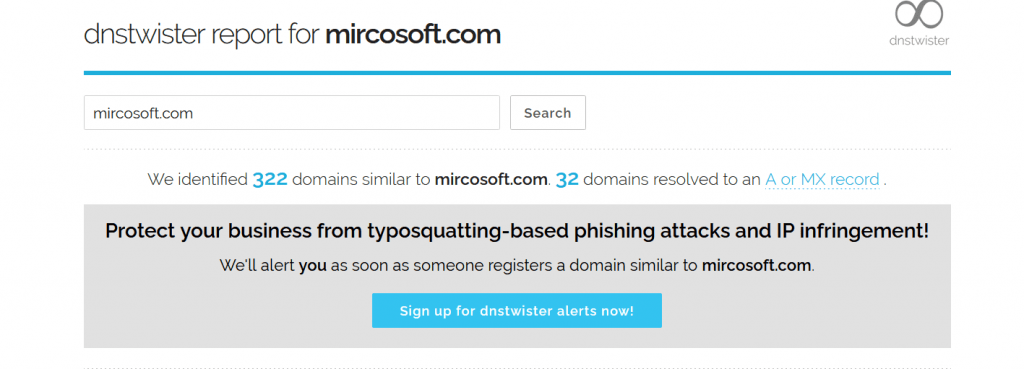
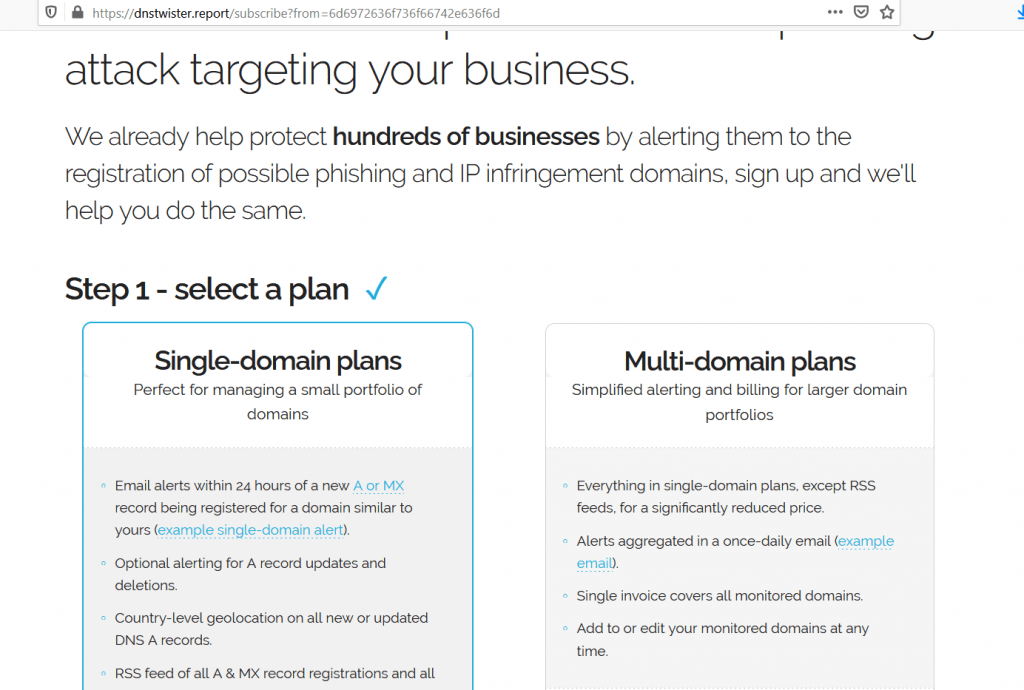
Signup on DNSTwist Reporter for alerts on the registration of possible phishing domains which is similar to your brand.
Happy Hunting !